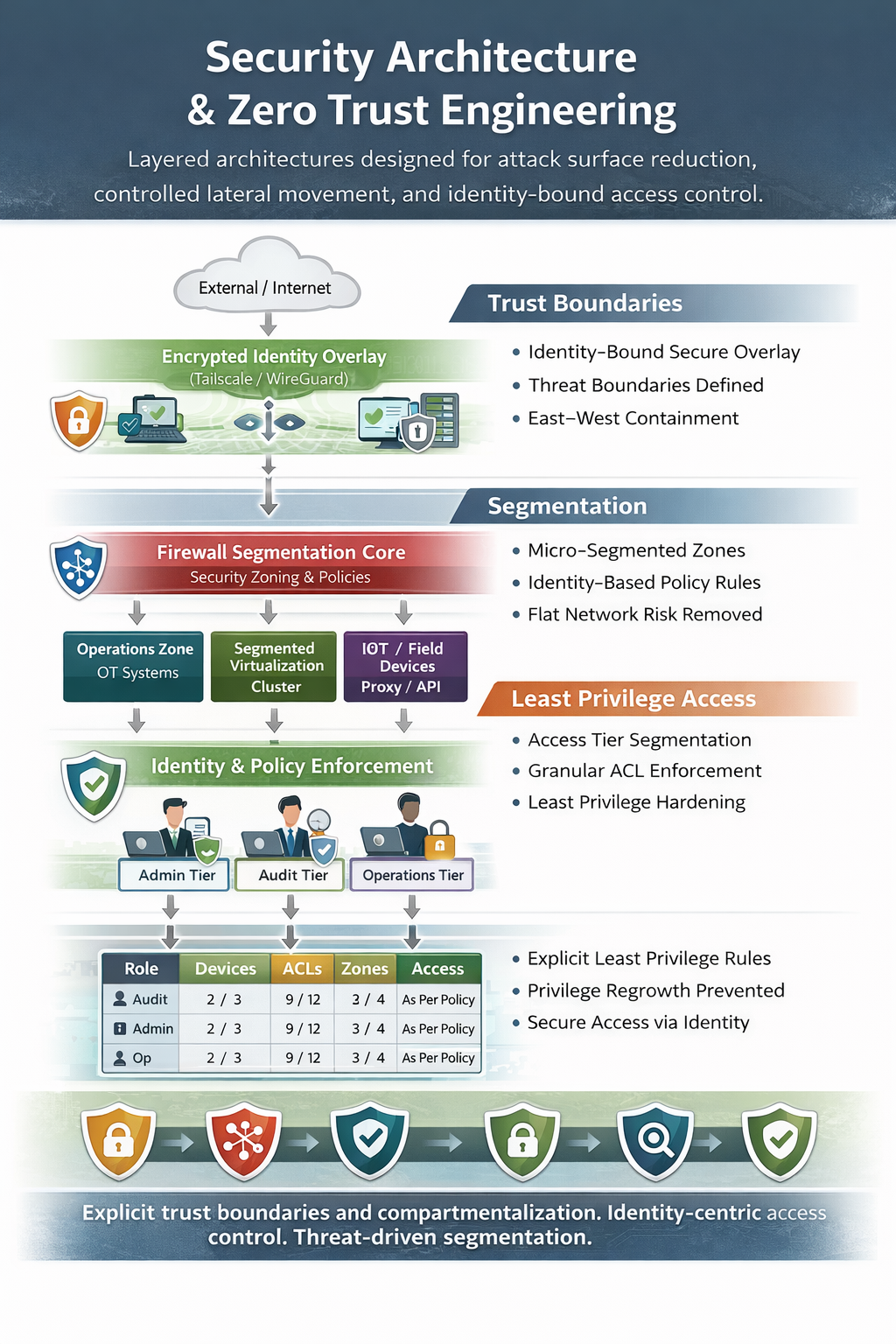
Security Architecture & Zero Trust Engineering
Design and implementation of defensible architectures aligned with Zero Trust principles, minimizing implicit trust and enforcing identity-bound access controls.
Capabilities:
Zero Trust Network Architecture (ZTNA) design
Identity-centric access control modeling
Trust boundary definition and enforcement
Zero Trust Network Architecture (ZTNA) design
Micro-segmentation strategy
East–West traffic restriction design
Least privilege policy engineering
Threat modeling (STRIDE / attack surface analysis)
Secure hybrid infrastructure design
Architectures are designed to prevent lateral movement, minimize blast radius, and enforce policy-driven access control across infrastructure layers.
Virtualization & Container Security Engineering
Hardened compute environments with strict workload isolation and controlled inter-service communication.
Virtualization Hardening:
Hypervisor isolation and attack surface reduction (KVM-based clusters)
Secure clustering and HA design using Proxmox
Network bridge segmentation and VLAN enforcement
Secure storage backends and access controls
RBAC policy design
Container Security:
Secure image lifecycle management
Runtime isolation & namespace hardening
Network namespace segmentation
Reverse proxy and ingress control
Secure orchestration patterns using Docker
Supply chain integrity validation
Focus: deterministic isolation, minimized cross-tenant exposure, and reduced attack propagation paths.
Network Security Engineering
Layered network design enforcing explicit traffic control across L2–L7.
Firewall & Routing Architecture:
Stateful inspection policy engineering
Multi-zone segmentation
Inter-VLAN access control modeling
NAT & asymmetric routing correction
IDS/IPS placement strategy
Secure gateway architecture with OPNsense
Secure Remote Access:
Identity-bound encrypted overlays using Tailscale
WireGuard-based secure mesh design
Exit-node compartmentalization strategies
Split vs full tunnel architecture analysis
Access tiering for untrusted devices
Segregation of management plane from data plane
Designed for environments requiring remote multi-client access with strict trust boundary enforcement.
Compartmentalized Infrastructure Design
High-assurance segmentation for multi-tenant, multi-client, or high-risk environments.
Engineering focus:
Risk-domain isolation
Perimeter reduction strategy
Privilege domain separation
VLAN + overlay trust alignment
Management plane isolation
Infrastructure-level blast radius containment
Applicable to:
Service providers
Financial services
Critical infrastructure
Regulated EU environments (NIS2-aligned)
Incident Response & Digital Forensics
Structured response with evidentiary integrity and post-compromise architectural correction.
Capabilities:
Host and network forensic acquisition
Log correlation & timeline reconstruction
TTP mapping against adversary frameworks
Root cause and lateral movement tracing
Containment architecture redesign
Post-incident hardening strategy
Objective: eliminate systemic weaknesses, not merely remediate artifacts.
Secure Systems Integration
Deployment of security-aligned software stacks within existing enterprise ecosystems.
Secure reverse proxy architecture
Identity provider integration
Infrastructure-as-Code hardening
Secure CI/CD considerations
Compliance-aware deployment models
Emphasis on minimizing misconfiguration risk and reducing configuration drift.